Published endpoints
Expose HTTP and non-HTTP services as globally reachable endpoints without opening inbound ports. Agents maintain outbound tunnels, and the edge routes incoming traffic to the upstream service.
rstream is a developer-first platform for zero-trust networking. Expose local and private services through outbound-only tunnels, with identity-based access, policy enforcement, and observability handled at the edge, without requiring a VPN.
Expose HTTP and non-HTTP services as globally reachable endpoints without opening inbound ports. Agents maintain outbound tunnels, and the edge routes incoming traffic to the upstream service.
Connect to services through client-only tunnels addressed by name or identifier. This fits internal access paths, fleet connectivity, and workflows where endpoints should not be publicly reachable.
Enforce identity and access policy at the entrypoint before traffic reaches upstream. rstream Auth, scoped tokens, mutual TLS, challenge mode, and IP or Geo restrictions can be applied consistently.
Use one connectivity model across protocols. HTTP 1.1, HTTP/2, HTTP/3 plus TLS, DTLS, and QUIC cover bytestream and datagram workloads, including legacy or custom protocols.
Serve users and systems close to where they run. Multi-region entrypoints keep routing centralized while agents stay lightweight and deployable across environments.
Understand behavior end to end. Connection logs capture the path and edge decisions, and metrics expose trends for throughput, latency signals, errors, and performance.
Learn the core building blocks behind tunnels, agents, and edge routing. Explore the docs.
Install the rstream CLI on a developer machine, server, or device where resources need to be exposed.
Authenticate, then select the project that will own endpoints and credentials.
Run rstream forward to publish a local port and obtain a forwarding address.
rstream is compatible with Linux, macOS and Windows. Get rstream now.
Built in Europe, rstream gives teams that prefer a European solution a straightforward option for private connectivity and identity-aware access.
Keep upstream services private. Agents connect outbound, reducing attack surface and removing the need for inbound firewall rules.
Protect agent-to-edge connectivity with encrypted transport. Published tunnel protocols can be terminated or forwarded based on tunnel configuration.
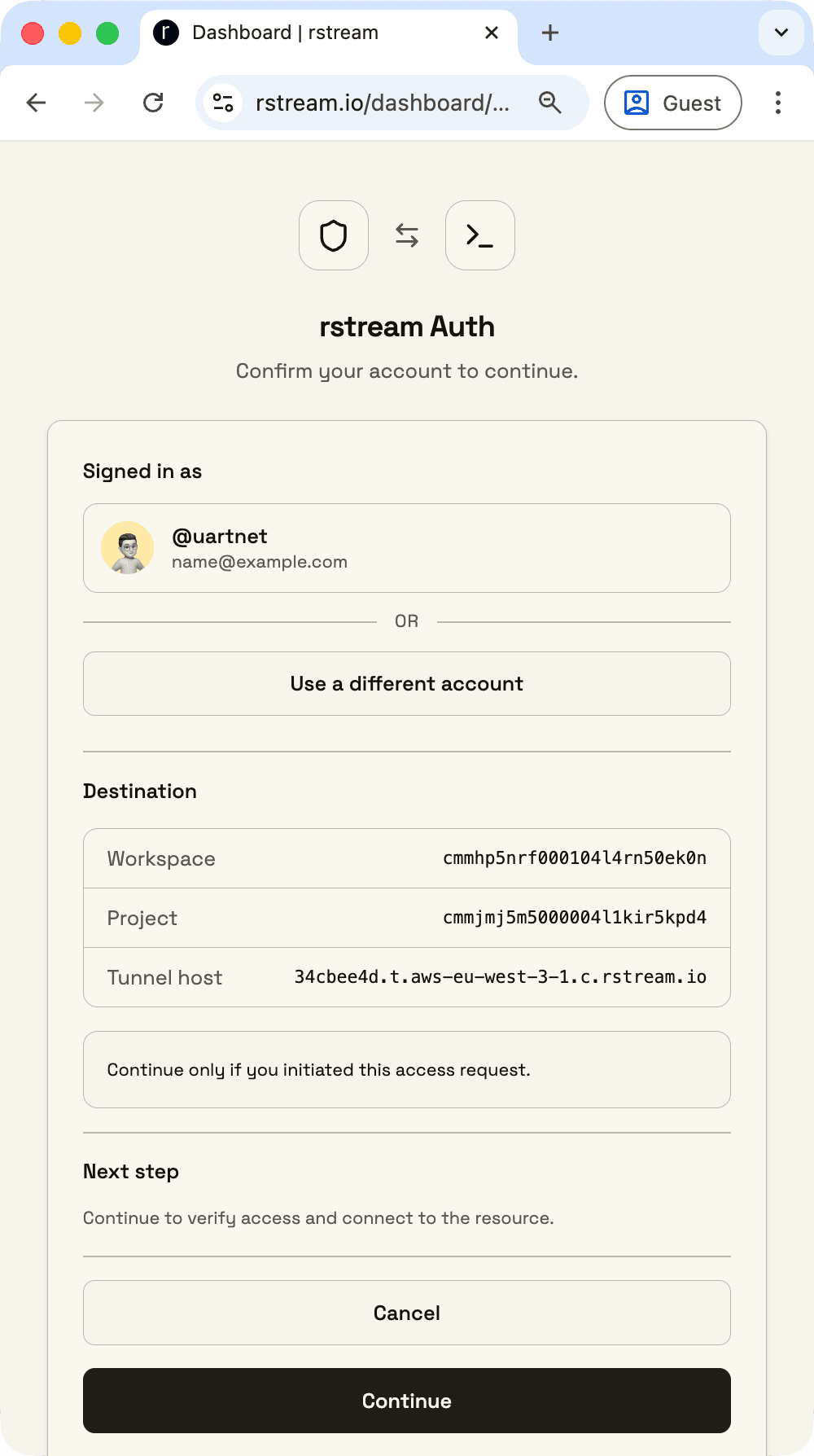
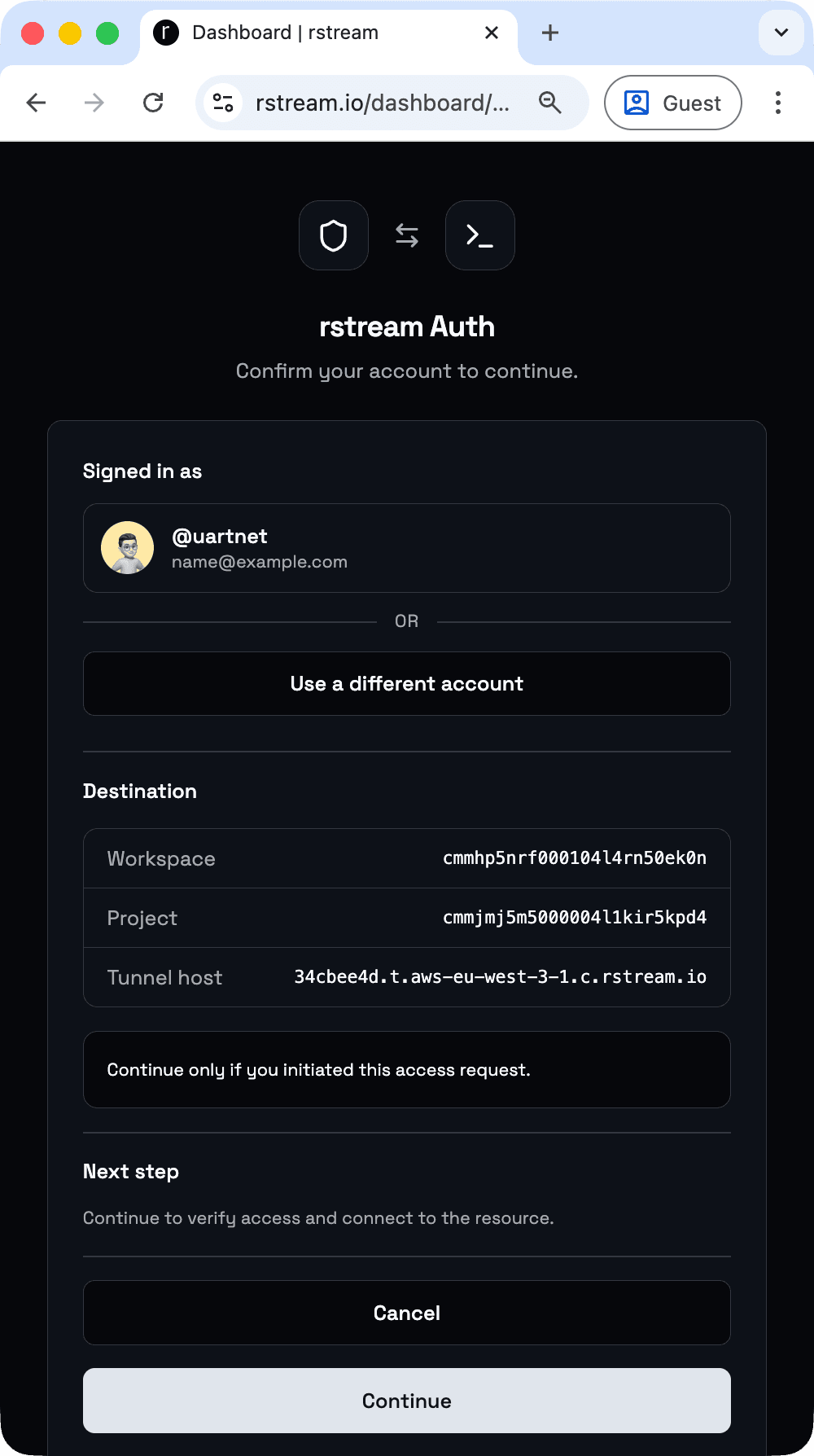
Use account-based browser authentication for operator and human access before requests are routed upstream.
Issue scoped credentials for discovery, creation, and access. Permissions can be narrowed to specific tunnels, labels, and access paths.
Restrict access to known networks with allowed IP ranges.
Apply geographic restrictions at the entrypoint for additional control.
Use client certificates for agent control-channel authentication and for published tunnel access policies.
Apply identity and access policy at the edge so published endpoints and private tunnels share one enforcement model across regions and environments.
Rotate and revoke credentials to respond to compromise and lifecycle requirements.
Dive deeper into zero-trust access, rstream Auth, tokens, and enforcement rules at the edge. Read security docs.
Clients
GET /image.svg
rstream edge network
accepting connection...
checking IP reputation...
checking geo policy...
verifying token...
routing upstream...
streaming response...
writing connection log...
Upstream
$ rstream expose 8080
forwarding: https://d76659d1.t.aws-eu-west-3-1.c.rstream.io
waiting for connections...
new connection
$ python -m http.server 8080
Serving HTTP on 127.0.0.1:8080
GET /image.svg HTTP/1.1" 200 -
Go deeper into tunnel types, protocols, and how traffic is forwarded. Explore tunnels.
Expose local services for demos, QA, collaboration, or homelab tooling without asking developers to reconfigure networks. A forwarding address makes a localhost service reachable in minutes.
Control identity-based access at the edge while keeping inbound ports closed. This reduces exposure, hides upstream addresses, and supports remote access to SSH, dashboards, and legacy services through a zero-trust access layer.
Operate devices and machines across networks using consistent access paths. Private tunnels and APIs can act as a signaling layer to discover endpoints and drive operational tooling.
Distribute work across runners or GPU machines with scoped credentials and auditable access. This supports pipelines where generated code and agents require controlled network reachability.
Handle low-latency coordination and datagram workloads with a consistent edge model. This fits WebRTC signaling, STUN and TURN-assisted connectivity, telemetry, interactive control channels, and other real-time systems that need identity and observability at the edge.
rstream is designed to work across stacks and environments, so the same building blocks can be applied to a wide range of workflows.
Declarative tunnels
Define tunnels as configuration that stays in sync with deployments. rstream reconciles desired state and applies updates as services change, using YAML, Docker labels, and Kubernetes custom resources. Protocols, upstream targets, publishing, identity, and access policy live in versioned configuration.
Declare protocol, upstream target, publishing, and access policy in a versioned specification.
Attach tunnel configuration to services through labels so tunnel state follows the runtime stack.
Expose Services with RstreamConnection and RstreamTunnel resources while the operator manages agents and status.
Keep tunnel state aligned as services change, avoiding drift and ad-hoc tunnel sprawl.
version: 1
tunnels:
- name: "http-server"
forward: "127.0.0.1:8080"
tunnel:
publish: true
protocol: "http"
labels:
app: "http-server"
http:
version: "http/1.1"
auth:
token: true
rstream: true
Move from ad-hoc setup to reconciled connectivity that stays aligned over time. Learn declarative tunnels.
Observability
Trace every request and connection end to end. Logs capture the connection path and enforcement decisions, while metrics expose trends for throughput, latency signals, and error rates over time.
Inspect the full connection path from downstream to upstream, including entrypoint decisions, protocol details, and timing signals.
Subscribe to connection activity through the API for dashboards, alerts, and operational tooling.
Deliver events to external systems without maintaining a streaming connection.
Track trends over time for throughput, latency signals, and error rates across services and environments.
No logs in this time range
Try a longer timeline or refresh.
Learn how to investigate incidents with connection logs and operational metrics. Learn observability.
rstream clients and SDKs
Integrate the rstream edge network directly into applications and services. The CLI and SDKs provide scriptable connectivity to the edge network, endpoint exposure, private tunnel dialing, and scoped credentials so access control can be handled in code.
Script tunnel workflows from CI, deploy jobs, and operational automation using the same open runtime code that powers the SDKs.
Reference implementation with the broadest feature and protocol coverage. The CLI is built from the Go codebase.
Build product integrations that need tunnels plus platform workflows, including API access and event-driven patterns.
Native integration for latency-sensitive services, agents, and gateways. Designed around the Boost.Asio asynchronous model.
#!/bin/bash
# Start a tiny HTTP server on :8080 that returns the hostname
python3 - <<'PY' &
import socket, http.server
h = socket.gethostname().encode()
class H(http.server.BaseHTTPRequestHandler):
def do_GET(self): self.send_response(200); self.end_headers(); self.wfile.write(h)
def log_message(self, *a): pass
http.server.ThreadingHTTPServer(("127.0.0.1", 8080), H).serve_forever()
PY
server_pid=$!
trap 'kill "$server_pid"' EXIT
# Expose a tunnel that forwards incoming traffic to local port 8080
rstream forward 8080
Start integrating rstream directly into an application using the CLI, SDKs, and examples. Explore integrations.
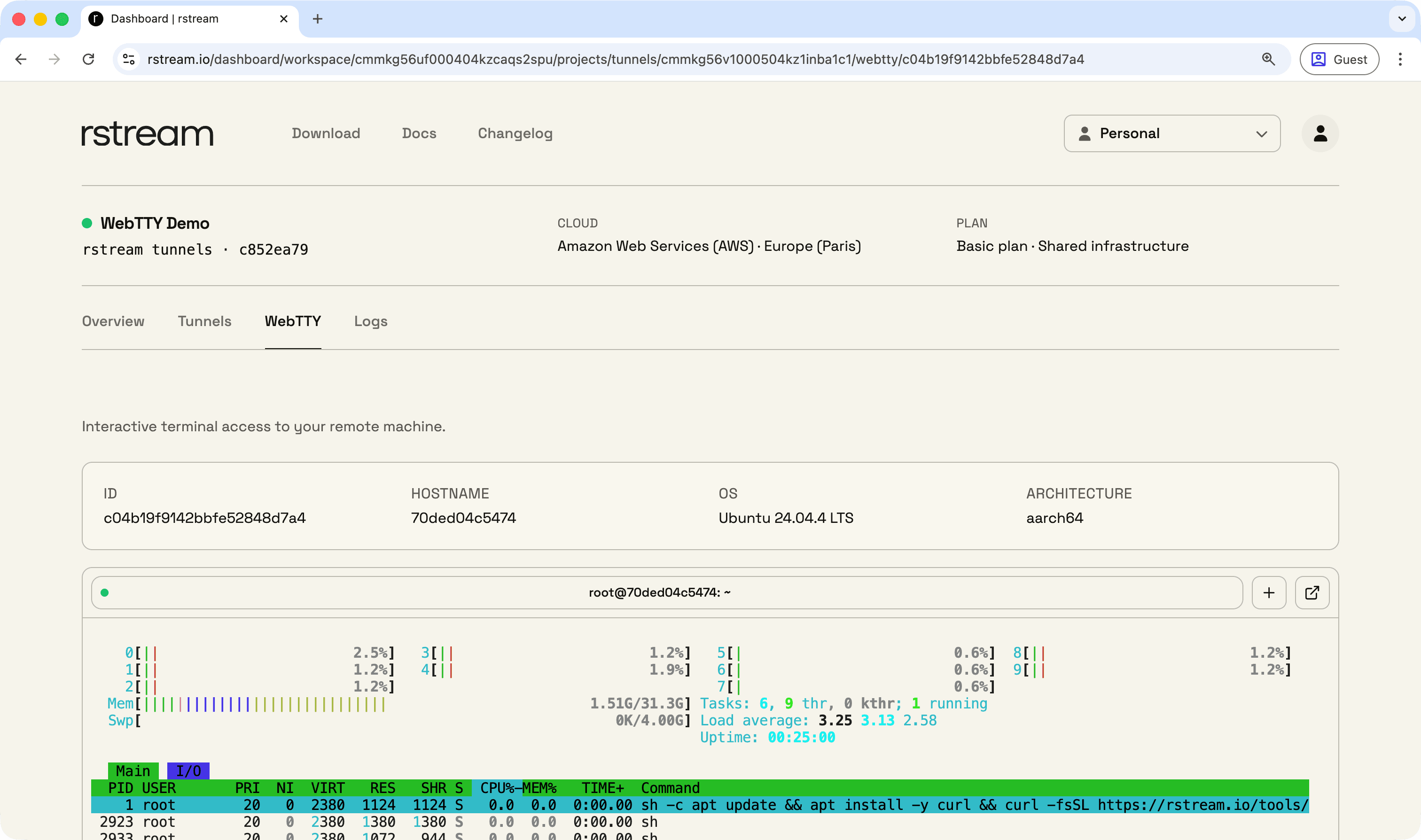
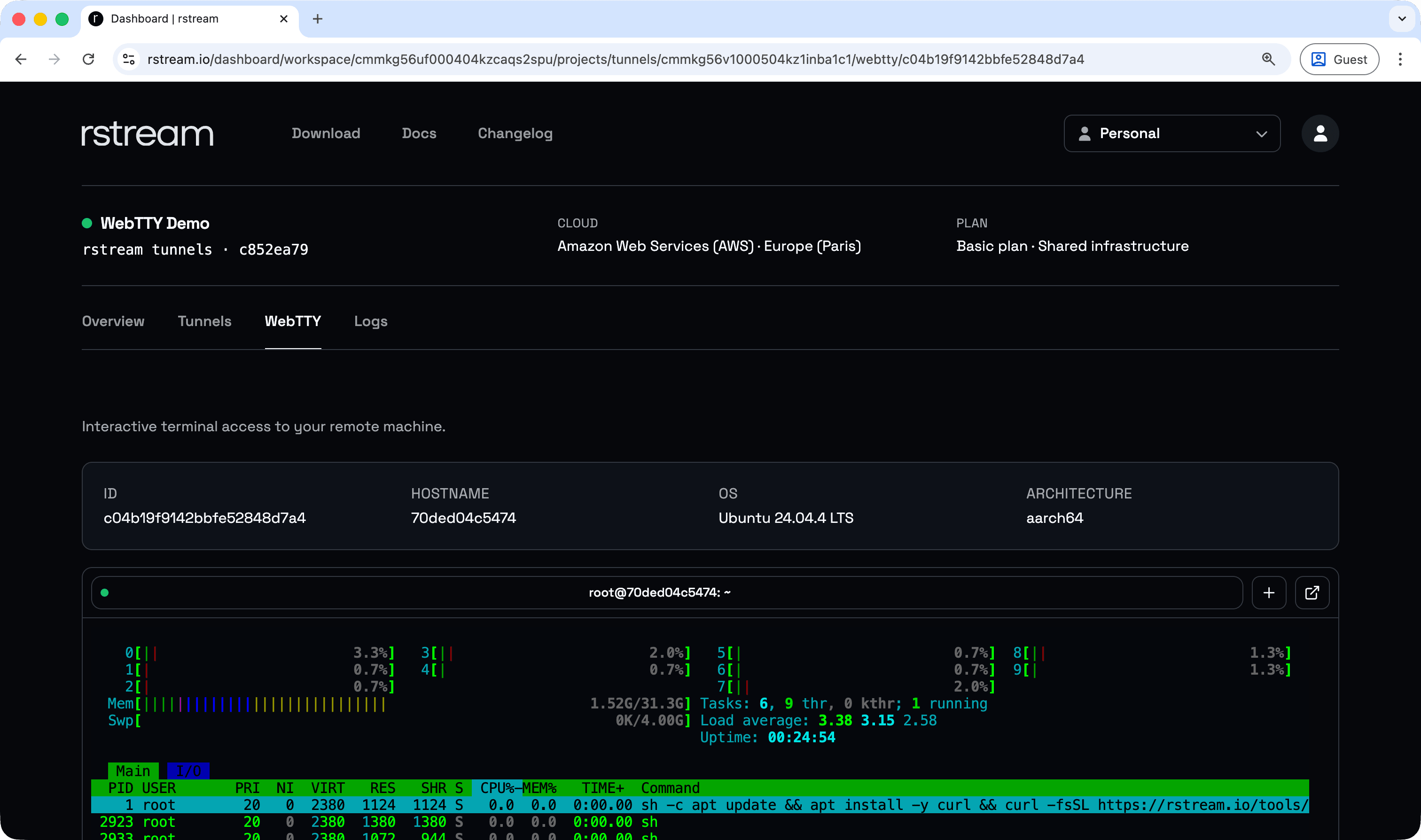
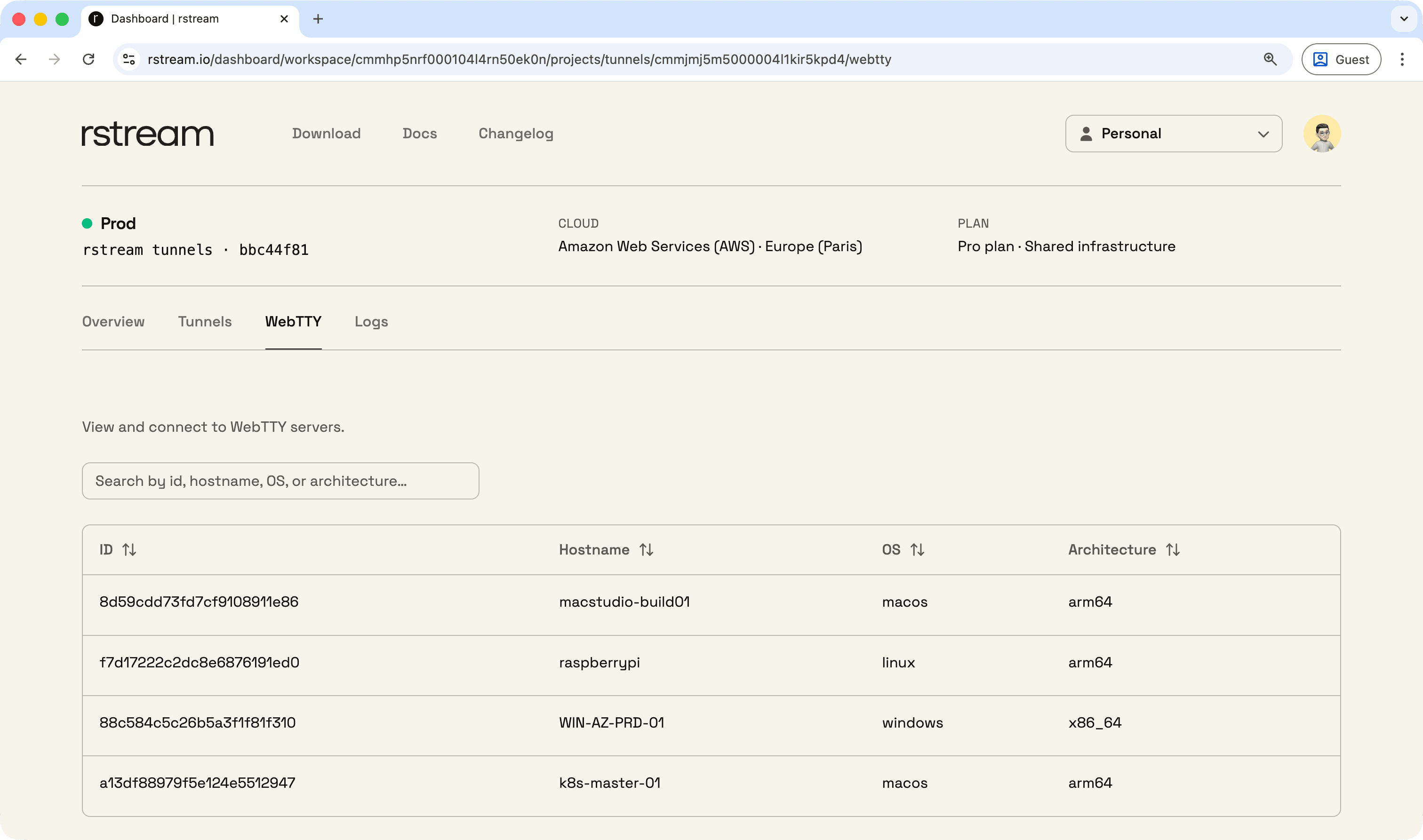
rstream WebTTY
rstream WebTTY provides browser-based terminal access for managing machines and fleets. It enables secure remote command-line access without inbound ports or network reconfiguration, and sessions can be opened from the web dashboard, the CLI, or an SDK integration with identity and policy enforced at the entrypoint.
Open remote terminal sessions directly from a browser, without requiring local SSH setup.
Use a consistent access path for machines and devices across environments, with identity and policy applied at the entrypoint.
Keep inbound ports closed. The WebTTY server establishes connectivity outbound.
Open sessions from the dashboard, from the CLI, or embed access paths into tooling through SDK integration.
root@a11c63224a2b:/# /bin/bash -i -c "$(curl -fsSL https://rstream.io/scripts/install-debian.sh)"
- detected curl
- installing gnupg for gpg verification...
Reading package lists...
Building dependency tree...
Reading state information...
debconf: delaying package configuration, since apt-utils is not installed
Setting up adduser (3.137ubuntu1) ...
Setting up libksba8:arm64 (1.6.6-1build1) ...
Setting up pinentry-curses (1.2.1-3ubuntu5) ...
Setting up libsqlite3-0:arm64 (3.45.1-1ubuntu2.5) ...
Setting up gnupg-l10n (2.4.4-2ubuntu17.4) ...
Setting up readline-common (8.2-4build1) ...
Setting up gnupg-utils (2.4.4-2ubuntu17.4) ...
Setting up libreadline8t64:arm64 (8.2-4build1) ...
Setting up gpgconf (2.4.4-2ubuntu17.4) ...
Setting up gpg (2.4.4-2ubuntu17.4) ...
Setting up gpg-agent (2.4.4-2ubuntu17.4) ...
Setting up gpgsm (2.4.4-2ubuntu17.4) ...
Setting up dirmngr (2.4.4-2ubuntu17.4) ...
Setting up keyboxd (2.4.4-2ubuntu17.4) ...
Setting up gnupg (2.4.4-2ubuntu17.4) ...
Setting up gpg-wks-client (2.4.4-2ubuntu17.4) ...
Processing triggers for libc-bin (2.39-0ubuntu8.7) ...
- installation summary:
- package name : rstream
- package channel : stable
- package version : latest
- os : ubuntu
- dist : noble
- arch : arm64
- installing apt-transport-https...For a live walkthrough, open the Web Remote Terminal demo.
rstream sandbox
rstream sandbox is an open source, general-purpose sandbox for running AI- and LLM-generated code under strong isolation. It is designed around isolation technologies such as gVisor, Kata Containers, and Firecracker microVMs, with filesystem and network access for real workloads plus multi-runner orchestration from a single host to a fleet. Self-hosted runners are free to run, with connectivity handled through rstream tunnels.
rstream sandbox is an open source, general-purpose sandbox runtime for AI- and LLM-generated code execution, including backend services, runners, and client libraries.
Use strong isolation strategies built around gVisor, Kata Containers, and Firecracker microVMs for untrusted and dynamically generated workloads.
Run generated scripts, agents, backend jobs, and tool workflows with filesystem and network access on native runners, in Docker-based environments, or in Kubernetes.
Schedule workloads across one host or a fleet. Self-hosted runners are free to operate, and connectivity between components is handled through rstream tunnels.
import { Sandbox } from "@rstreamlabs/sandbox";
import * as dotenv from "dotenv";
async function main() {
try {
// Create new session
const session = await new Sandbox().sessions.create();
// Run python code and wait for the result
const { stdout, exitCode } = await session.run({
code: `print("Hello, World!")`,
plugin: "python",
});
// Print outputs
console.log(stdout);
console.log(`Exit code: ${exitCode}`);
// Close the session to free up resources
await session.close();
} catch (error) {
console.error(
JSON.stringify({ error: error?.message ?? String(error) }, null, 2),
);
}
}
dotenv.config({ path: [".env"] });
main();
rstream sandbox will be available later this year.
The rstream engine community edition is a self-hosted engine runtime. It is free to run, does not require an rstream account, and can operate fully offline within a private network perimeter.
Run the community edition at no cost while keeping deployment and operations under your control.
Deploy the engine inside your network boundary, including fully offline deployments.
Use the same tunnel concepts, client workflows, and SDK patterns for published endpoints and private tunnels.
Deploy on bare metal, Docker, or Kubernetes to match existing platform standards.
Deploy the community edition of the engine for full operational control. Self-host the engine.
Expose services as globally reachable endpoints without opening inbound ports.
Dial client-only connectivity by tunnel name or identifier for non-public access paths.
Publish HTTP services through the edge with consistent routing and policy.
Enable multiplexed HTTP semantics where clients and configuration allow it.
Enable modern HTTP/3 behavior for latency-sensitive client traffic.
Support HTTP upgrade flows for long-lived connections such as WebSocket.
Support WebTransport over HTTP/3 for low-latency bidirectional traffic.
Publish TLS services as endpoints without exposing upstream networks.
Publish datagram workloads with DTLS for UDP-style encrypted protocols.
Publish QUIC services for modern datagram-capable transport semantics.
Handle TCP-like stream workloads with ordered, reliable delivery.
Handle UDP-like message workloads for interactive and real-time patterns.
Expose services as globally reachable endpoints without opening inbound ports.
Dial client-only connectivity by tunnel name or identifier for non-public access paths.
Publish HTTP services through the edge with consistent routing and policy.
Enable multiplexed HTTP semantics where clients and configuration allow it.
Enable modern HTTP/3 behavior for latency-sensitive client traffic.
Support HTTP upgrade flows for long-lived connections such as WebSocket.
Support WebTransport over HTTP/3 for low-latency bidirectional traffic.
Publish TLS services as endpoints without exposing upstream networks.
Publish datagram workloads with DTLS for UDP-style encrypted protocols.
Publish QUIC services for modern datagram-capable transport semantics.
Handle TCP-like stream workloads with ordered, reliable delivery.
Handle UDP-like message workloads for interactive and real-time patterns.
Carry legacy or custom bytestream/datagram protocols using the same tunnel model.
Gate access using tokens at the entrypoint before traffic is routed upstream.
Scope discovery, creation, and access down to tunnel properties and access paths.
Use account-based browser authentication at the entrypoint for operator access.
Require a challenge step at the entrypoint to reduce automated abuse.
Authenticate runtime clients with certificates and require certificates on published tunnel entrypoints.
Restrict access to known networks using IP ranges at the entrypoint.
Apply geographic constraints at the entrypoint as an additional policy layer.
Forward TLS end-to-end when upstream must own certificates and ALPN negotiation.
Terminate TLS at the edge when the endpoint needs edge enforcement and visibility.
Inspect the end-to-end path and entrypoint decisions per request/connection.
Track trends for throughput, latency signals, and error rates over time.
Carry legacy or custom bytestream/datagram protocols using the same tunnel model.
Gate access using tokens at the entrypoint before traffic is routed upstream.
Scope discovery, creation, and access down to tunnel properties and access paths.
Use account-based browser authentication at the entrypoint for operator access.
Require a challenge step at the entrypoint to reduce automated abuse.
Authenticate runtime clients with certificates and require certificates on published tunnel entrypoints.
Restrict access to known networks using IP ranges at the entrypoint.
Apply geographic constraints at the entrypoint as an additional policy layer.
Forward TLS end-to-end when upstream must own certificates and ALPN negotiation.
Terminate TLS at the edge when the endpoint needs edge enforcement and visibility.
Inspect the end-to-end path and entrypoint decisions per request/connection.
Track trends for throughput, latency signals, and error rates over time.
Subscribe to activity through the API for dashboards, alerts, and tooling.
Deliver the same event signals to external systems without a streaming connection.
Attach structured metadata to tunnels to drive discovery and access patterns.
Filter and locate tunnels by labels for fleet and multi-tenant workflows.
Define protocol, upstream, publishing, and policy in versioned configuration.
Attach tunnel intent to services so connectivity follows the container runtime.
Expose Services with custom resources and status-driven reconciliation.
Keep runtime tunnel state aligned with declared configuration as services change.
Use multiple regions for entrypoints and routing close to users and systems.
Use rstream tunnels as a signaling layer for WebRTC through labels, authenticated APIs, and real-time event streams.
Provide browser-based terminal access for machines and fleets without inbound ports.
Use the managed STUN and TURN service for ICE connectivity, with project-bound credentials issued by the API or derived locally.
Subscribe to activity through the API for dashboards, alerts, and tooling.
Deliver the same event signals to external systems without a streaming connection.
Attach structured metadata to tunnels to drive discovery and access patterns.
Filter and locate tunnels by labels for fleet and multi-tenant workflows.
Define protocol, upstream, publishing, and policy in versioned configuration.
Attach tunnel intent to services so connectivity follows the container runtime.
Expose Services with custom resources and status-driven reconciliation.
Keep runtime tunnel state aligned with declared configuration as services change.
Use multiple regions for entrypoints and routing close to users and systems.
Use rstream tunnels as a signaling layer for WebRTC through labels, authenticated APIs, and real-time event streams.
Provide browser-based terminal access for machines and fleets without inbound ports.
Use the managed STUN and TURN service for ICE connectivity, with project-bound credentials issued by the API or derived locally.
Full protocol and transport details, including tunnel modes and compatibility notes. View specifications.
Ideal for individuals and small projects. Securely expose resources with basic requirements.
Free
Designed for small teams requiring full protocol support, strong security controls, and support.
$49 / month
Limited launch offer — locked forever for early users
For organizations requiring isolated infrastructure, no quotas, and enterprise-grade security controls.
Custom
Prices are listed in US dollars. Applicable taxes may be added. Invoices are provided in dashboard after purchase. Subscriptions may be cancelled at any time.
Compare plans, limits, and feature availability. View pricing.
For more detailed information, refer to the documentation.
Start deploying your first endpoint